I thought it would be a good time to talk a little bit about the “constellation” of honeypots that I have going right now, and what statistics I have gathered on their activity. My Dionaea honeypots are organized under the name GRAB, and the first GRAB honeypot was located in NYC. Several days later I set up the same kind of honeypot and VPS in Frankfurt, and on July 30th I created two more in Singapore and Bangalore.

I’m not completely satisfied with this constellation just yet – I feel like there are a few gaps here that would be relevant to me. I’m glad that I have coverage in the US and Europe but I’d like to have some coverage in LATAM and Africa. The main reason that I was able to get the VPS coverage in these current locations so quickly was that this is where Digital Ocean has datacenters, and it’s incredibly easy to get a system set up with them (I set up both of the new VPSs and honeypots simultaneously in about 10 minutes). I feel that I absolutely need to get something created in the Russian Federation, and have been looking into options for this. Africa would be interesting, particularly around the Horn, but I have no idea about what the state of hosting is for this region. LATAM would be interesting, and I wonder if there is something good available for hosting in Argentina or Mexico. I’m hoping that the GRAB system I have in Singapore is sufficient for covering East/Southeast Asia and Australia, but we’ll see how that turns out.
My reasoning is that I imagine that while there are malware that will propagate world-wide (and I’ve already seen some samples show up in both NYC and Frankfurt), I imagine there might be some more regional samples that are targeted to a specific region or even a specific country or userbase that I could collect by having honeypots in various locations. I’m also interested to see the levels of activity in the various regions over time, which is what I’m going to get into next, starting with the NYC honeypot.
Some quick notes on how this data was obtained and graphed – I have my Dionaea honeypots set up to store data in sqlite databases. There are a few options out these for graphing (e.g., there’s a recipe in the Malware Analyst’s Cookbook for using gnuplot) but I used DionaeaFR. I thought that the best instructions for setting this up were found at Koen Van Impe’s site but even so I had some issues as far as getting it to run on my system. What I ultimately did was follow those instructions but use the most up to date versions of the dependencies (such as nodejs) when I did my install as the exact instructions posted there didn’t work on my system. I also ran “npm install -g promise” in addition to installing less as this was mentioned on another website.
New York City
Connections: 617,440
Unique IPs: 12,586
Files Downloaded: 48

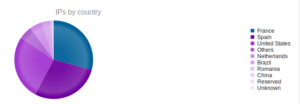
Since this is my first time doing this, I don’t have much to compare these results with, however that seems like a LOT of connections. I’m not shocked to see that most of the connections came from the United States but it was interesting to see that the most unique IP addresses came from France, Spain and the USA. For all that activity, not too many binaries recovered, but even so I’m backed up on analysis. Romania was unexpected (0.71% of the total IPs).

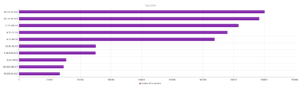
A mix of services, but interesting to see that the vast majority of activity came in over UPnP.

Therefore, I suppose it’s not a shock that the most activity also came through port 1900, the UDP port for UPnP.
The top IP address (with 80,000 connections) can be linked back to Tinet in Germany, though I’m not getting much out of this whois record, just info about Tinet. VirusTotal finds no domains resolving to that IP address and actually puts it in France. Similarly, the next one on the list, 84.16.14.189, links back to Telefonica in Spain (VirusTotal also has not resolved anything to this address, though it does not find any location info on this IP). This isn’t showing too much, as it’s sort of the equivalent of tracing an IP back to Level III or Comcast. The ninth IP on the list, 185.62.190.87, lists info as BlazingFast LLC in Kiev Oblast, Ukraine. They seem to be a hosting provider, maybe I should set up a honeypot with them…nothing about this IP address in VirusTotal. Not much comes up about any of these addresses.
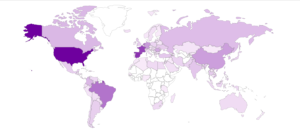
Here’s a map showing the attacker locations:

Next is the Frankfurt honeypot – It’s interesting that this honeypot was created several days after the NYC honeypot, and yet it had more activity (but fewer files downloaded).
Frankfurt
Connections: 702,786
Unique IPs: 10,896
Files Downloaded: 35

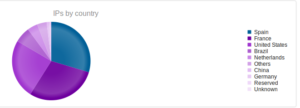
Pretty similar proportions to the stats from the NYC honeypot. There’s a certain country that doesn’t show up on either graph, which is surprising. Maybe it’s lumped into “others”, but keep in mind that the lowest ranks on this graph make up less than 1% (e.g., Germany on this chart is only 0.91%) so I’m surprised that these others ranked high enough to show up here.
Services is really very similar to the NYC results, UPnP being the most popular by a huge margin, along with port 1900:

Looking at the IP addresses from Frankfurt, there are several overlaps, either in terms of the same IP or just the same subnet. Only 204.88.128.14 and 213.140.43.126 are new.

204.88.128.14 is interesting – its whois record says “Santa Clara County Office of Education” in San Jose, CA. I’m wondering why so many connections would be coming from here? Some searching showed that someone’s already added this IP to FireHOL’s blocklist. I wonder what the story is with this one. 213.140.43.126 is just another Telefonica IP address, nothing too interesting there.
Here’s another map of the attackers, with an alternate view of the same data as well: